The Risks of Misconfiguration on Internet-Facing Assets and Its Impact on Data Protection
These misconfigurations expose personally identifiable information (PII) of users and customers, raising serious concerns about data protection.
Advisory: The Risks of Misconfiguration on Internet-Facing Assets
Executive Summary
These misconfigurations expose personally identifiable information (PII) of users and customers, raising serious concerns about the effectiveness of data protection measures and revealing a troubling trend of mere paper compliance with regulations like NDPR.
Evidence of Misconfigurations
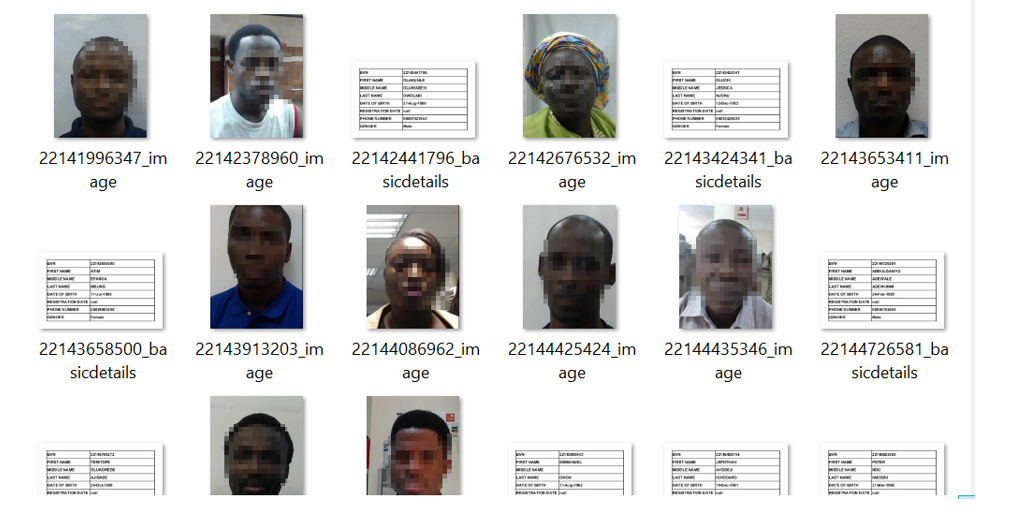
Example of exposed database interfaces found during our assessment.
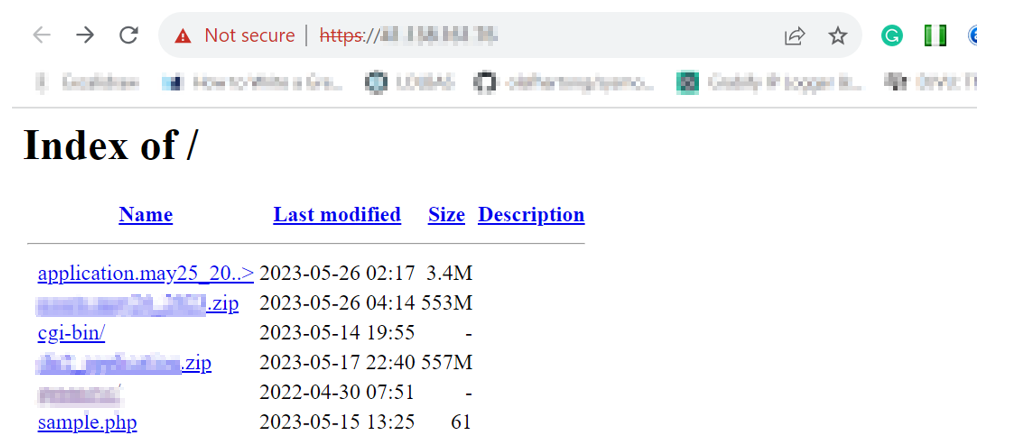
Additional evidence showing sensitive data exposed through misconfigured services.
Common Misconfigurations Observed
Database Exposures
- MongoDB instances without authentication
- Elasticsearch clusters publicly accessible
- Redis servers exposed to internet
Cloud Storage
- Misconfigured S3 buckets
- Azure blob storage with public access
- Google Cloud Storage ACL issues
API Vulnerabilities
- APIs without authentication
- Excessive data in API responses
- Debug endpoints in production
Data at Risk
| Data Type | Frequency | Impact |
|---|---|---|
| Customer PII | Very Common | High |
| Financial Records | Common | Critical |
| Health Information | Occasional | Critical |
| Internal Documents | Common | Medium |
| Credentials | Occasional | Critical |
Regulatory Implications
NDPR Compliance
Many organizations claim NDPR compliance but fail basic security hygiene:
- Consent without Security: Collecting consent but not protecting data
- Paper Policies: Written policies not implemented in practice
- No Incident Response: Unable to detect or respond to breaches
- Lack of Encryption: Data stored and transmitted without encryption
Recommendations
Technical Measures
- Conduct regular security assessments
- Implement proper access controls
- Use encryption for data at rest and in transit
- Deploy security monitoring solutions
- Regular configuration audits
Organizational Measures
- Security awareness training
- Clear data handling procedures
- Incident response planning
- Regular compliance audits
- Third-party security assessments
Conclusion
Compliance is not just about documentation—it requires actual implementation of security controls. Organizations must move beyond paper compliance to genuine data protection.
WhiteHat NG Data Protection Advisory