Advisory: Increased APT Activities in Nigeria
Since mid-2022, there has been a notable rise in Advanced Persistent Threat (APT) activities along the shores of Nigeria.
Critical Severity
This vulnerability requires immediate attention. Affected systems should be patched or mitigated as soon as possible.
Alert: Increased APT Activities in Nigeria
Executive Summary
Since mid-2022, there has been a notable rise in Advanced Persistent Threat (APT) activities along the shores of Nigeria. Recent data from supporting Security Operations Centers (SOC) and Managed Security Service Providers (MSSP) confirms this trend.
Threat Intelligence Evidence

Malware analysis showing sophisticated techniques used by APT groups targeting Nigerian organizations.
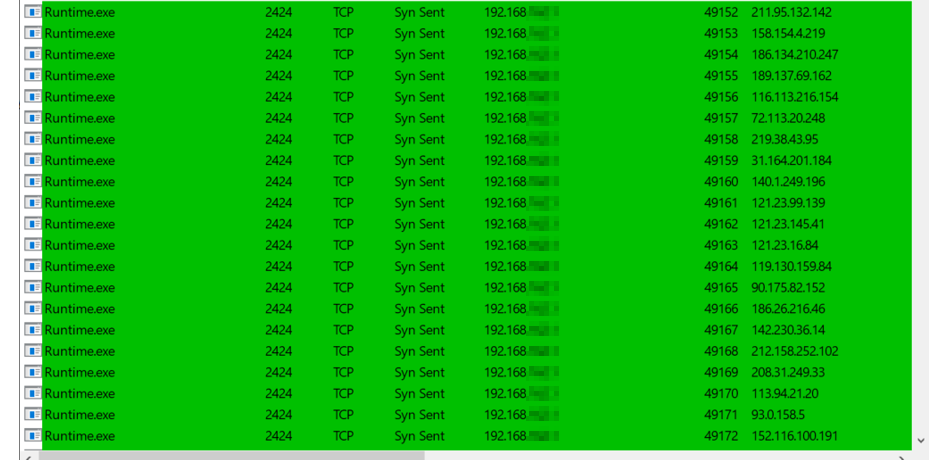
Command and control infrastructure identified during our investigation.
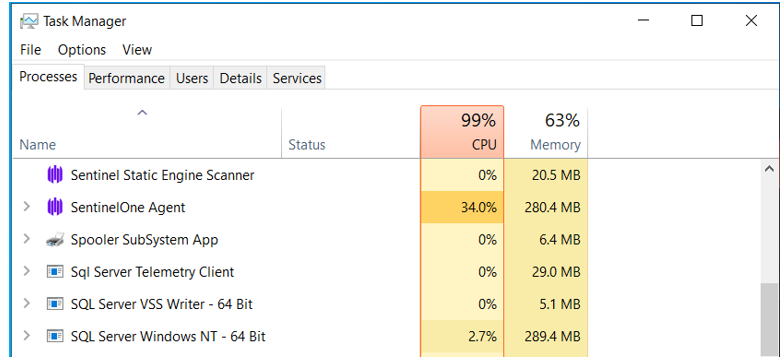
Additional indicators showing persistence mechanisms deployed by threat actors.
Threat Landscape
Observed APT Groups
Multiple sophisticated threat actors have been identified conducting operations in Nigerian cyberspace:
- State-sponsored actors conducting espionage
- Financially motivated APT groups
- Hacktivists with political motivations
Target Sectors
| Sector | Threat Level | Primary Objectives |
|---|---|---|
| Government | Critical | Intelligence gathering |
| Oil & Gas | High | Industrial espionage |
| Financial Services | High | Financial theft |
| Telecommunications | High | Data collection |
| Critical Infrastructure | Medium | Reconnaissance |
Tactics, Techniques, and Procedures (TTPs)
Initial Access
- Spear phishing campaigns
- Exploitation of public-facing applications
- Supply chain compromise
Persistence
- Custom malware deployment
- Living-off-the-land techniques
- Compromised credentials
Objectives
- Long-term access for intelligence collection
- Data exfiltration
- Infrastructure mapping
Recommendations
For Organizations
- Implement defense-in-depth security architecture
- Deploy advanced endpoint detection and response (EDR)
- Conduct regular threat hunting activities
- Establish incident response capabilities
- Share threat intelligence with peers and authorities
For Security Teams
- Monitor for indicators of compromise (IOCs)
- Analyze logs for anomalous behavior
- Implement network segmentation
- Regular security assessments
Collaboration
WhiteHat NG is working with government agencies and private sector partners to track and mitigate these threats.
WhiteHat NG Threat Alert